Metadata: The Hidden Information Trail
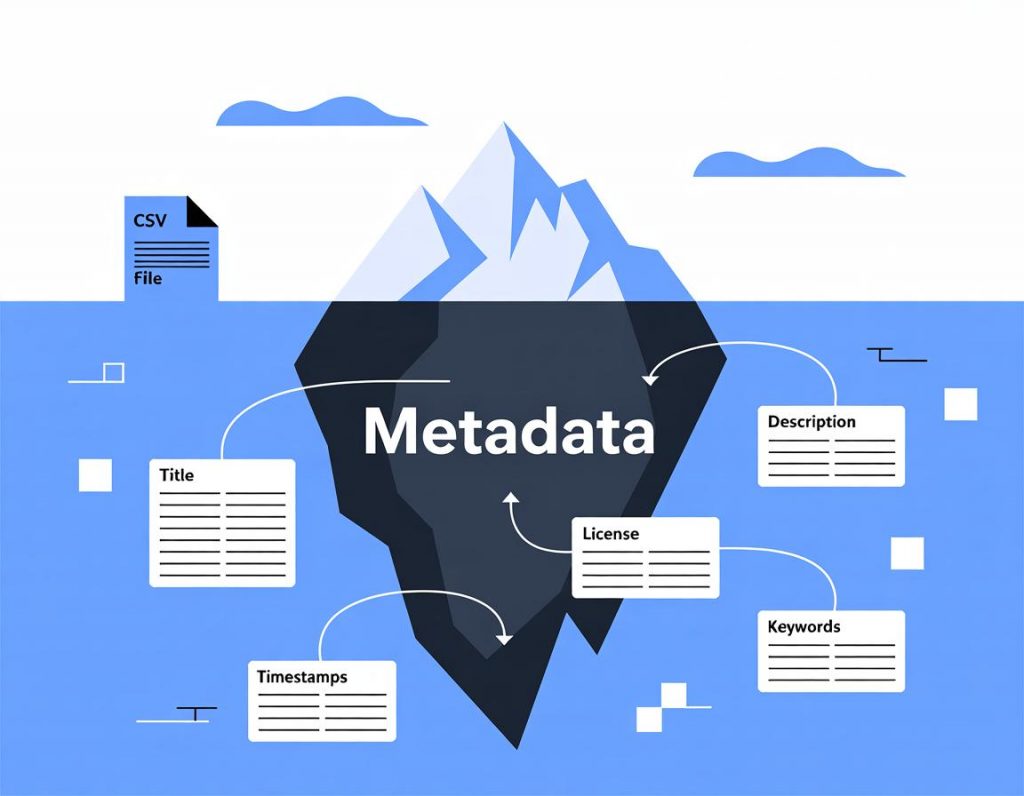
You might encrypt your messages, use privacy tools, and carefully protect your data. But there’s another information trail you might not have considered: metadata. Sometimes called “data about data,” metadata can reveal surprisingly intimate details about your life. Let’s explore what it is, why it matters, and how to think about protecting it.
What Exactly Is Metadata?
Metadata is information about your communications and activities, as opposed to the content itself. When you send an email, the content is what you write in the message. The metadata is everything else: who you sent it to, when you sent it, what device you used, your location, how large the email was, and more.
Think of it like a letter. The content is what’s written inside. The metadata is the information on the envelope: sender and recipient addresses, the postmark showing when and where it was mailed, the size and weight of the envelope. Even if the letter is sealed, the envelope tells a story.
Why Metadata Matters More Than You Think
Former NSA director Michael Hayden famously said, “We kill people based on metadata.” That stark statement reveals how valuable metadata can be for revealing patterns and relationships. Even without knowing what you said, metadata can reveal who your friends are, what your habits are, where you go, and what matters to you.
Researchers have demonstrated that metadata alone can reveal:
Your social network and closest relationships
Your daily routines and travel patterns
Your political and religious affiliations (inferred from who you communicate with)
Your health concerns (inferred from which doctors you call)
Your financial situation (inferred from communication patterns)
All of this without ever knowing the content of a single message.
Types of Metadata
Communication Metadata: Who you contact, when, how often, and from where. Phone records, email headers, messaging app contacts – all generate metadata about your social connections.
Location Metadata: GPS coordinates embedded in photos, cell tower connections, WiFi access points detected by your phone. This data creates detailed maps of your movements.
Device Metadata: What device you use, its unique identifiers, what operating system and apps you have installed, when they’re updated. This creates a fingerprint that can identify you across different services.
Behavioral Metadata: When you’re active online, your browsing patterns, what types of content you engage with. This reveals habits and interests even without knowing specifically what you viewed.
The Problem with Metadata Collection
Unlike content surveillance, which typically requires warrants or legal process in democratic countries, metadata collection often faces fewer legal restrictions. The reasoning has been that metadata is “less private” than content. But research shows this distinction is artificial – metadata can be more revealing than content.
Consider this example: the content of your communications might not reveal that you’re job hunting. But metadata showing calls to headhunters, visits to competing companies’ offices, and increased LinkedIn activity paints a clear picture.
How Services Use Your Metadata
Every online service collects metadata. Social media platforms track who you interact with, when you’re active, and what content you engage with. Search engines record your queries along with timing and location information. Fitness apps track your routes and exercise patterns.
This metadata powers recommendation algorithms, targeted advertising, and service improvements. But it also creates detailed profiles that can be sold, shared, or potentially leaked. The Cambridge Analytica scandal showed how metadata analysis can reveal psychological profiles and influence behavior.
Protecting Against Metadata Exposure
Metadata is harder to protect than content because it’s often necessary for systems to function. But you can reduce metadata exposure:
For Communications: Use services designed to minimize metadata collection. Signal, for example, stores minimal metadata about its users. Email, by design, creates extensive metadata trails.
For Location: Turn off location services when not needed. Remove GPS data from photos before sharing (many tools can “strip” this metadata). Be aware that even without GPS, other information can reveal location.
For Browsing: Use privacy-focused browsers and search engines. Consider tools like Tor that obscure connection metadata. Regularly clear cookies and browsing data.
For Devices: Use privacy settings to limit what information apps can access. Understand that device identifiers can track you across services even without logging in.
The Tor Approach to Metadata
Tor specifically addresses metadata protection by hiding the connection between source and destination. When you browse through Tor, websites don’t see your real IP address, and your ISP doesn’t see what websites you visit. This protects connection metadata, though other metadata (like browser fingerprints) requires additional protection.
This is why the Tor Browser includes additional privacy features beyond just the Tor network – it works to minimize all forms of identifying metadata.
Metadata in Different Contexts
Academic Research: Researchers often have access to rich metadata without accessing actual content. This enables valuable studies about social networks, information flow, and behavior patterns while potentially protecting privacy. However, “anonymized” metadata can sometimes be re-identified.
Journalism: Protecting source metadata is as important as protecting source identity. A journalist might encrypt communications with a source, but if metadata reveals the connection, the source could still be identified.
Activism: In repressive environments, who you communicate with (metadata) can be as dangerous as what you say (content). This is why activists in sensitive situations use tools that protect both.
The Legal Landscape
Laws protecting metadata lag behind its capabilities for revealing private information. In many jurisdictions, metadata receives less legal protection than content. This creates a gap where extensive information about individuals can be collected with minimal oversight.
Some recent legal developments have begun recognizing metadata’s sensitivity. The EU’s GDPR treats metadata as personal data deserving protection. But globally, legal frameworks often haven’t caught up to the reality of what metadata reveals.
Thinking Critically About Metadata
Understanding metadata helps you make informed privacy decisions. When evaluating a privacy tool or service, ask not just about content protection but about metadata handling. Does the service collect metadata? How long is it stored? Who has access to it? Is it shared or sold?
For students studying privacy, security, or data science, metadata offers fascinating insights into how information can be revealing in non-obvious ways. It’s a reminder that privacy isn’t just about keeping secrets – it’s about controlling information about yourself, including information you might not realize you’re sharing.
The metadata problem shows why privacy is multifaceted. Encrypting your messages is important, but it’s not the whole story. True privacy requires protecting both what you say and the patterns of your communication, location, and behavior.