Understanding Digital Pseudonymity vs Anonymity
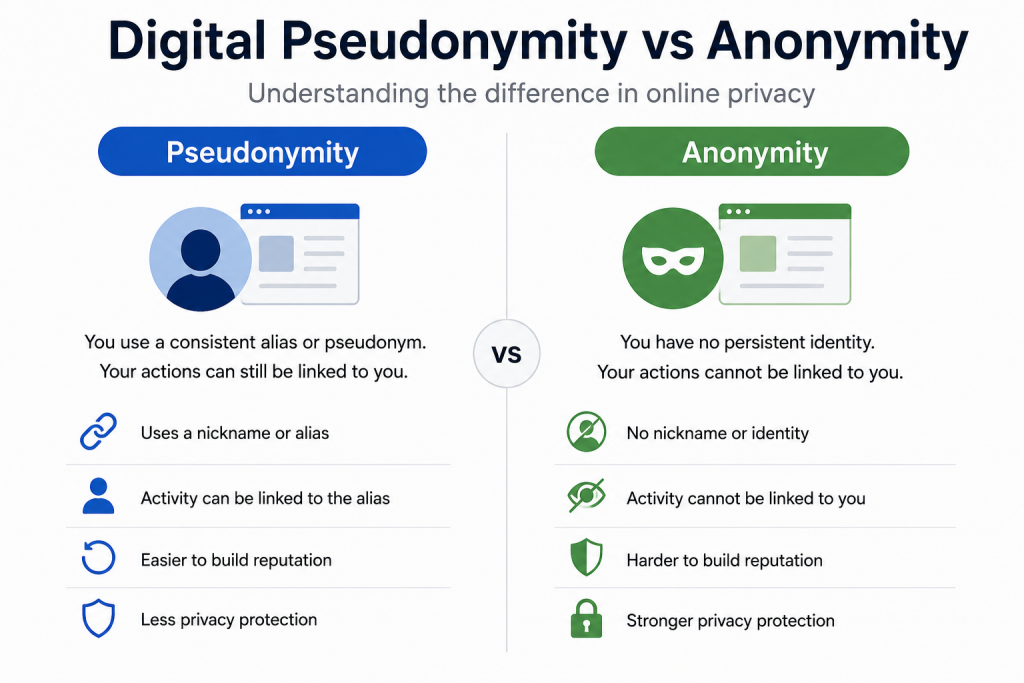
In discussions about online privacy, people often use “anonymity” and “pseudonymity” interchangeably. But they’re actually quite different, and understanding the distinction helps you make better choices about protecting your identity online. Let’s break down what each means and when you might want one versus the other.
Defining Anonymity
Anonymity means you can’t be identified at all. When you’re truly anonymous, no one – including the service you’re using – knows who you are. There’s no way to link your actions to your real-world identity or even to other actions by the same anonymous person.
Think of anonymous online activities like dropping cash in a donation box. Nobody knows who donated, and there’s no way to connect the donation to the donor. Each donation is completely separate and unconnected.
True anonymity online is difficult to achieve. It typically requires tools like Tor, careful operational security, and avoiding any identifying information. Even then, perfect anonymity is more theoretical than practical for most users.
Defining Pseudonymity
Pseudonymity means using a consistent false identity or handle. You’re not using your real name, but you’re building a persistent identity under your pseudonym. People can recognize and interact with your pseudonym over time, but ideally they can’t connect it to your real identity.
Think of authors who publish under pen names. George Eliot (real name Mary Ann Evans) built a reputation under her pseudonym. Readers knew George Eliot’s work but didn’t necessarily know who the person behind the name was. The pseudonym had continuity and reputation while protecting the author’s privacy.
Key Differences
Persistence: Anonymous actions leave no consistent trail. Pseudonymous actions are linked to a persistent identity, just not your real one.
Reputation: You can build reputation under a pseudonym. Your consistent identity lets people trust you over time. With pure anonymity, there’s no way to build trust or reputation.
Linkability: Pseudonymous activities can be linked together (that’s the point of the persistent identity). Anonymous activities should be unlinkable.
Deanonymization risk: If a pseudonym is ever connected to your real identity, all activities under that pseudonym can be attributed to you. Anonymous activities, if properly done, can’t be connected even if other activities are deanonymized.
When Anonymity Is Appropriate
True anonymity makes sense when:
Whistleblowing: When revealing information could endanger you, and there’s no need for ongoing communication
Anonymous surveys or research: When collecting data where identity would bias results or create risks
Voting: Where we specifically want to prevent connecting individuals to their choices
Browsing sensitive topics: Researching medical conditions, legal questions, or other private matters
One-time actions: When there’s no need for a persistent identity
The key is that you don’t need persistence or reputation, and you want maximum protection against identification.
When Pseudonymity Makes More Sense
Pseudonymity is better when:
Building online communities: You want to participate consistently while protecting your real identity
Professional separation: Keeping personal and professional lives separate without giving up identity entirely
Creative work: Publishing under a pen name while building readership
Political activism: Organizing while protecting against harassment or retaliation
Online gaming: Building reputation in a community without revealing real identity
The common thread is wanting both protection and persistence – a consistent identity that isn’t your real one.
The Technical Side
Achieving strong anonymity requires:
Tools like Tor that hide your IP address and location
Not logging into any accounts connected to your real identity
Avoiding patterns of behavior that could identify you
Not reusing the same anonymous identity across sessions
Being careful about metadata that could reveal your identity
Maintaining pseudonymity requires:
Creating accounts that aren’t linked to your real information
Potentially using Tor or VPNs to prevent linking the pseudonym to your IP address
Being careful not to reveal identifying information through your pseudonymous activities
Keeping your real and pseudonymous activities completely separate
The Risks of Pseudonymity
Pseudonyms can be deanonymized. If you accidentally reveal identifying information under your pseudonym – mention your hometown, your profession, unique experiences – someone might connect the dots to your real identity. Once that link is made, everything you did under that pseudonym is exposed.
This has happened to many people. Bloggers writing under pseudonyms were identified through small details they mentioned. Online activists were traced through metadata their pseudonymous accounts generated. Even careful people sometimes slip up over years of pseudonymous activity.
Combining Both Approaches
Some activities benefit from combining anonymity and pseudonymity. You might:
Create a pseudonym but access it only through Tor for additional protection
Use anonymous channels to establish trust before revealing a pseudonym for ongoing communication
Compartmentalize different pseudonyms for different activities, accessed through different methods
Use anonymity for high-risk actions and pseudonymity for community building
The key is understanding which protection you need for which activities.
Legal Considerations
In most democratic countries, you have the right to speak pseudonymously. Court cases have recognized that anonymity and pseudonymity in speech are protected, just as anonymous pamphleteering was protected in early America.
However, this protection isn’t absolute. Courts can sometimes compel service providers to reveal pseudonymous users’ identities, particularly in legal proceedings. The bar for this varies by jurisdiction and circumstance.
Social Norms and Pseudonymity
Different online communities have different norms about pseudonymity. Gaming communities typically expect pseudonyms. Professional networks like LinkedIn expect real names. Understanding and respecting these norms helps you participate appropriately while protecting yourself.
Some platforms (like Facebook) require “real names,” though their enforcement is inconsistent and controversial. These policies can endanger people who have legitimate reasons for using pseudonyms: domestic abuse survivors, activists, LGBTQ+ individuals, etc.
For Students and Researchers
Understanding this distinction helps in several ways:
Research ethics: When conducting research involving people, knowing whether you need anonymity or can accept pseudonymity affects your study design.
System design: If you’re building online platforms, understanding these concepts helps you create appropriate privacy protections.
Critical analysis: When evaluating privacy tools or policies, you can assess whether they provide appropriate protections for their intended use.
Personal practice: You can make informed decisions about when to use which approach in your own online activities.
The Future of Digital Identity
As online and offline lives increasingly merge, questions about anonymity and pseudonymity become more complex. Biometric identification, AI-powered behavior analysis, and extensive data collection make both harder to maintain.
At the same time, growing awareness of privacy issues has led to stronger protections in some areas. The tension between identification and privacy will likely continue shaping technology and policy for years to come.
Understanding the difference between anonymity and pseudonymity helps you navigate these complex waters, making informed choices about when and how to protect your identity online.